- Top
- Service list
- PG Multi-Payment Service
- Security solution
- Vulnerability Assessment (GMO Cyber Security by Yerae)
Vulnerability Assessment
(GMO Cyber Security by Yerae)
▼ What is Vulnerability Assessment (GMO Cybersecurity by Yerae)?
Vulnerability diagnosis is a series of processes that find vulnerabilities (security weaknesses) in company systems and software and evaluate their risks and impacts. Vulnerability diagnosis is one of the important methods for strengthening security, and it has become indispensable in recent years when cyberattacks are becoming more sophisticated.
What is a vulnerability?
Vulnerabilities are information security flaws and weaknesses hidden in web applications, smartphone apps, software, cloud platforms, etc.
Vulnerabilities can be caused by a variety of causes, including bugs in the software, improper configuration, poor security policies, and unauthorized operations.
Background to the need for vulnerability assessment
Financial damage or loss of credibility
If the vulnerability is left unaddressed, it can be exploited when targeted by an attacker, resulting in website tampering, unauthorized access, leakage of important information such as personal information, credit card information, and confidential information, and intrusion into the corporate network. Such events can result in financial damage or damage to the reputation and goodwill of individuals and companies. In order to prevent such vulnerabilities from being exploited, it is desirable to conduct vulnerability assessments of systems every quarter ~ one year.
Examples of financial damage risk
Liability Risk
Risk of being claimed for damages due to leakage of customer information or system outage due to cyber attack
Cost Risk
Risks related to investigating the cause and scope of damage caused by cyberattacks, recovery, and implementation of measures to prevent recurrence

Profit Risk
Risk of suspension of the company's business and loss of profits until countermeasures are taken due to cyber attacks
Purpose of vulnerability assessment (risk and impact assessment)
The purpose of vulnerability assessment is to find vulnerabilities in systems, software, etc., and to assess their risks and impact.
In addition, by fixing vulnerabilities that are judged to be high-risk and have a high impact, it is possible to improve system security and prevent damage from exploitation.
As mentioned above, if a vulnerability is left unaddressed, it can be exploited by malicious actors and lead to financial damage and loss of trust. Before that happens, you need to identify vulnerabilities and fix them to keep your system secure.
■Security measures for EC operators
The "Credit Card Security Guidelines," which are practical guidelines for the obligation of security measures stipulated in the Installment Sales Act, describe the policy as follows. Please be aware that there is a movement in the e-commerce industry to make it mandatory to implement basic security measures, including vulnerability assessments.
・Current status: Declaration of the implementation status of security measures (trial)
All EC merchants must implement their own security measures before applying for a new merchant contract, and contact the card company (acquirer) or PSP (payment processing company) at the time of contract application. Company) and conclude a merchant contract with the card company (acquirer).
・Future: Mandatory basic security measures
"Credit card paymentIn the "Report of the Study Group on Strengthening System Security Measures" (January 20, 2023), as an immediate measure to strengthen leakage countermeasures of EC merchants, it is mandatory to take basic security measures against vulnerabilities in the system of EC merchants and the EC site itself (measures against deficiencies in system settings (PW management, etc.), vulnerability diagnosis and countermeasures, antivirus, etc.) 2024. It is required to be added to this guideline by the end of the fiscal year.
Types of vulnerability assessments and what to diagnose
Types of vulnerability assessments
Vulnerability Assessment can be conducted in the following ways:
- (1) Automated diagnosis: A method of scanning networks and systems using automated tools to detect known vulnerabilities.
- (2) Manual diagnosis: A method in which experts manually use characteristic patterns to find vulnerabilities
- (3) Hybrid: A hybrid method of manually conducting vulnerability diagnosis while using tools
Target of vulnerability assessment
The scope of vulnerability diagnosis is expanding more and more due to the emergence of new technologies such as web applications, smartphone applications, PC software, middleware, OS, network equipment, cloud platforms, IoT devices, and smart contracts used in blockchains.
Differences from penetration testing
Vulnerability assessment and penetration testing are both methods of assessing the security of a system, but they have different goals and approaches.
While vulnerability diagnosis aims to visualize the presence or absence of vulnerabilities, penetration testing finds vulnerabilities and verifies whether they can actually be exploited.
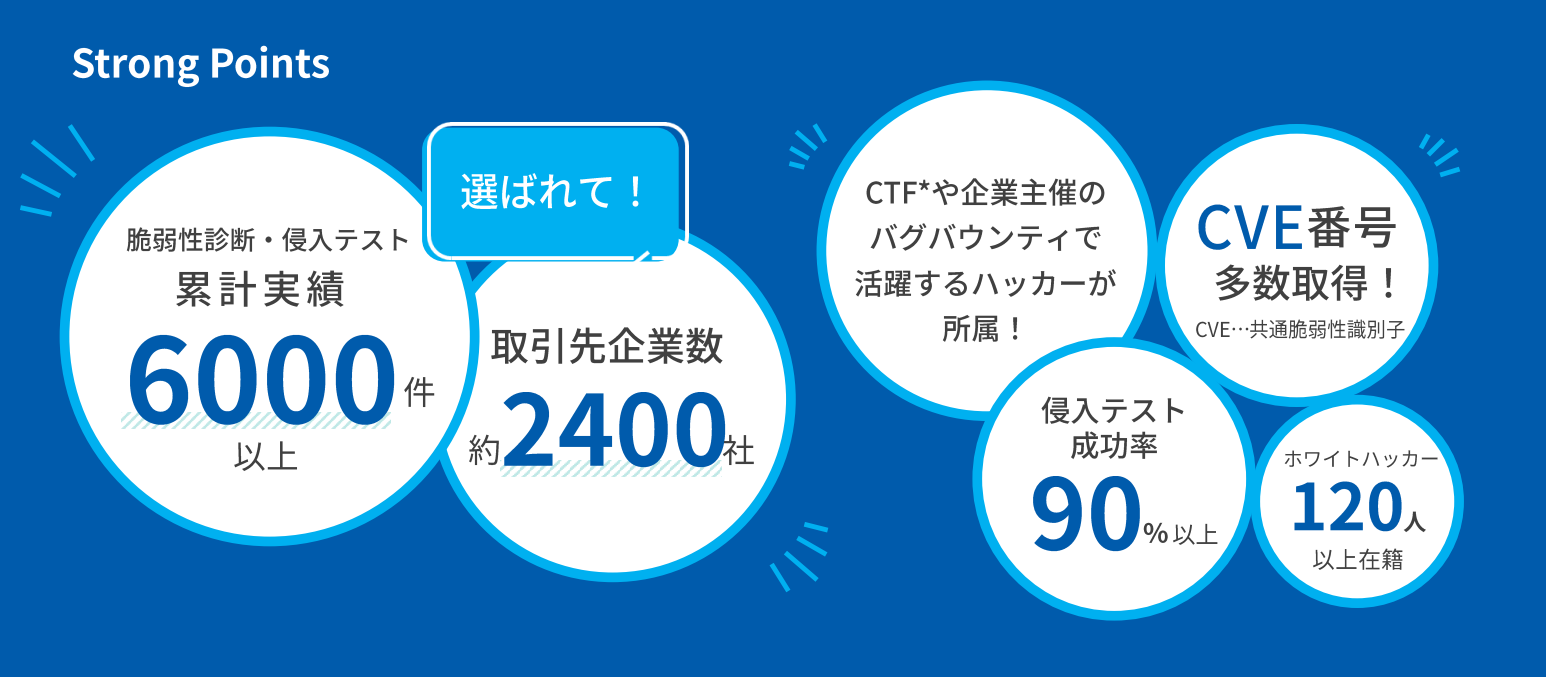
Features of GMO Cybersecurity by Yerae
Highest quality at the lowest price
Engineers belonging to GMO Cybersecurity by Yerae have participated in hacking contests held around the world and have achieved good results.
By continuing to update the latest and more sophisticated hacking technology, we are able to propose specific protection technologies and methods that companies need from the perspective of attackers.
In addition, we have realized that we can provide diagnostic technology at an inexpensive price by effectively utilizing the asset of abundant diagnostic Actual and improving work efficiency using AI.
How to choose a vulnerability assessment related service
【By request】Developer service lineup
* Web application diagnosis and diagnosis content are equivalent.
お問合せはこちらSimple Diagnosis Service "GMO Cyber Attack Net de Diagnosis"
GMO Cyber Attack Net de Diagnosis is a tool that is categorized as ASM (Attack Surface Management) recommended by the Ministry of Economy, Trade and Industry. Since it is possible to visualize vulnerabilities and grasp countermeasures inexpensively and easily, it is possible to respond to issues such as not knowing what to start with and not having the budget to spend on countermeasures.

This service is applicable when the introduced EC site is operated by a corporation.
If the introductory EC site is operated by an individual, please check here.


